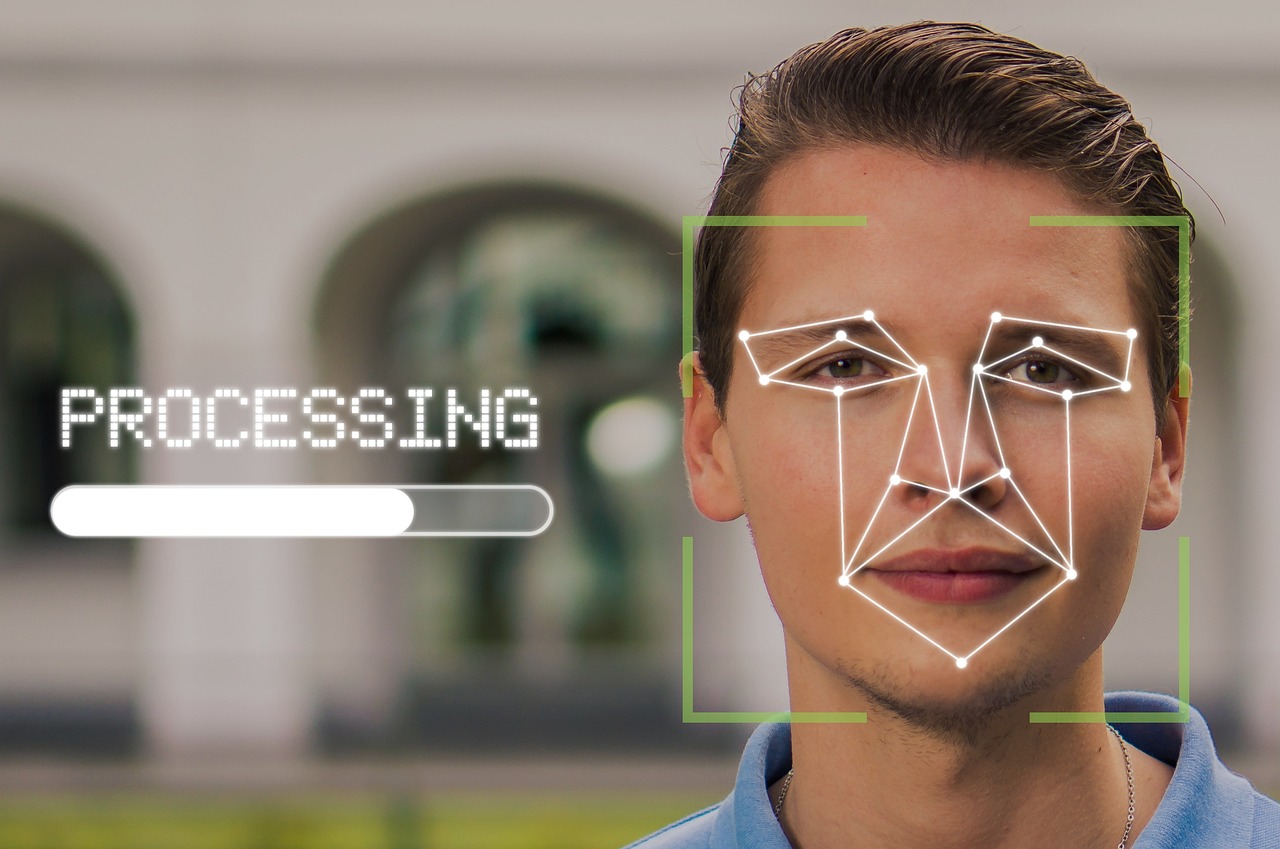
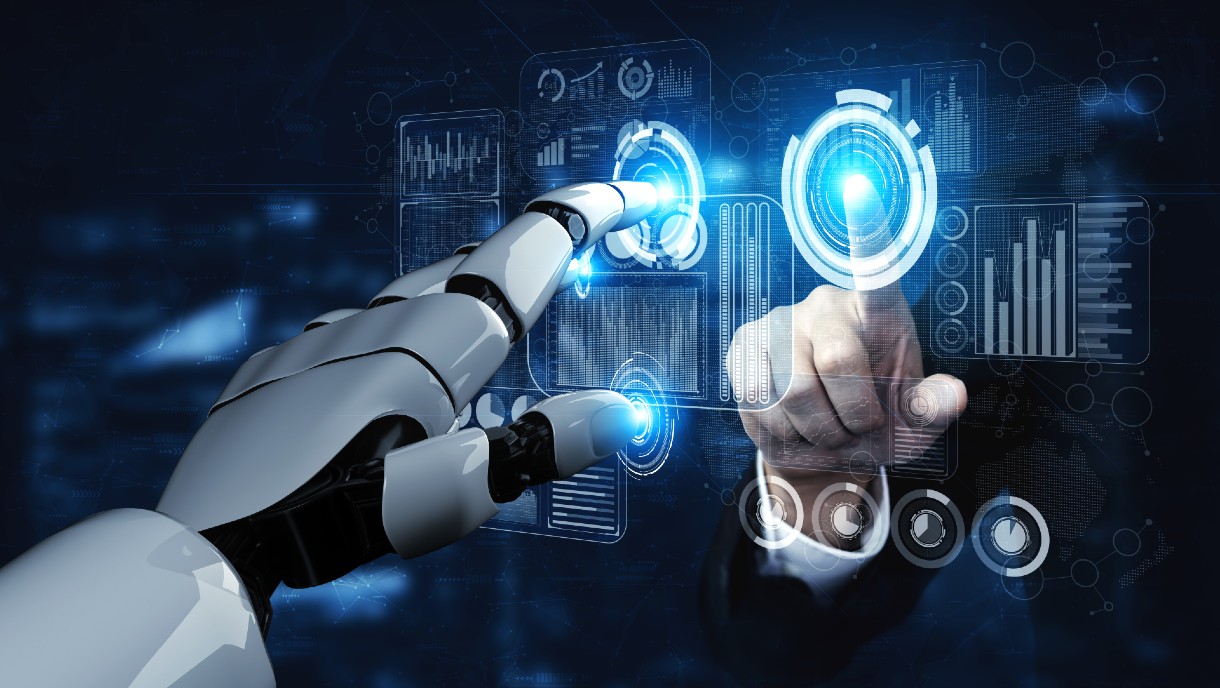
The ever-growing reliance on digital technology necessitates robust cybersecurity measures. As cybersecurity threats evolve and become more sophisticated, traditional password-based authentication methods are struggling to keep pace, leaving sensitive data...
Subscribe to our Blog
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et.
[gravityform id="13" title="false" description="false" ajax="true" ]