Contactless biometric technology is not new. However, in recent months, we have seen a steep rise in the use of contactless technology in business operations. This is so because contactless...
Identity Management
Meet the OLOID team at RSA Conference™ 2024 from 6th-9th May ’24 at Booth #6380, Moscone Center, San Francisco. Click here to book a meeting.
Meet the OLOID team at RSA Conference™ 2024 from 6th-9th May ’24 at Booth #6380, Moscone Center, San Francisco. Click here to book a meeting.
Meet the OLOID team at RSA Conference™ 2024 from 6th-9th May ’24 at Booth #6380, Moscone Center, San Francisco. Click here to book a meeting.
No More Posts
No more pages to load
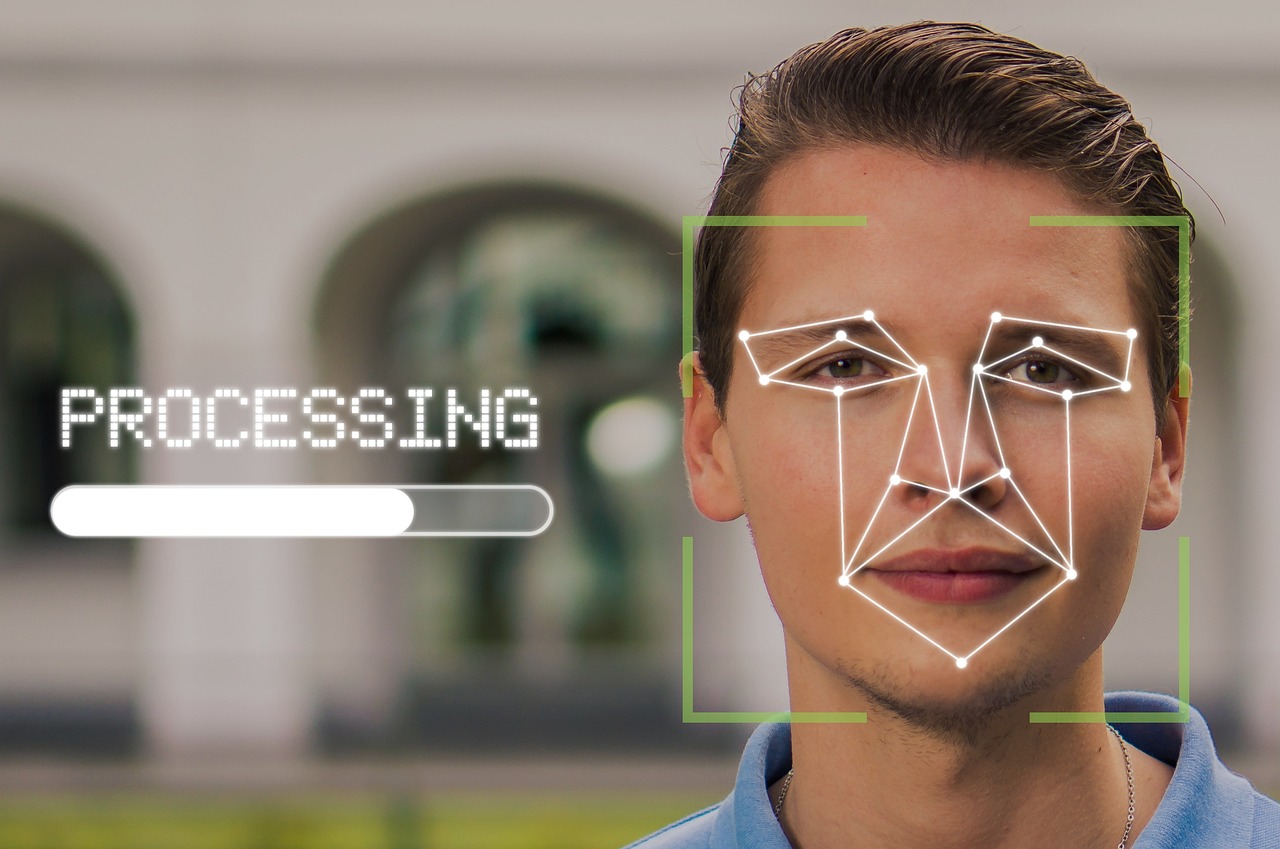
Facial Recognition
In our contemporary, fast-paced world, the need for security and convenience has reached a paramount status in nearly every facet of daily life. The advent of facial authentication, boasting an astonishing accuracy rate of up to 99.97%, stands as a…

Facial Recognition
Traditional methods of authentication, such as passwords and PINs, are increasingly vulnerable to sophisticated hacking techniques. As a result, there’s a growing demand for more robust security measures that can adapt to the evolving threat landscape. One such solution gaining…

Passwordless Authentication
In an era plagued by increasingly sophisticated cyber threats, relying solely on traditional authentication methods like passwords is akin to leaving the front door of your digital fortress wide open. This vulnerability underscores the critical importance of adopting multi-factor authentication…

Passwordless Authentication
In today’s digital landscape, the importance of secure authentication cannot be overstated. With cyber threats on the rise and traditional password-based systems proving increasingly vulnerable, there’s a pressing need for robust authentication standards. Enter FIDO and FIDO2 – two key…

Oloid – blogs
Ensuring the safety of people and assets is vital in our increasingly connected world. Whether in public spaces or private enterprises, robust physical security is essential to guard against theft, damage, and acts of terrorism. Fortunately, advancements in technology, particularly…

Oloid – blogs
In an era defined by digital transformation and ever-evolving cyber threats, the traditional approach to user authentication is facing unprecedented challenges. Password-based systems, once the cornerstone of digital security, are increasingly proving inadequate in safeguarding sensitive information against sophisticated cyber…

Passwordless Authentication
The ever-growing reliance on digital technology necessitates robust cybersecurity measures. As cybersecurity threats evolve and become more sophisticated, traditional password-based authentication methods are struggling to keep pace, leaving sensitive data vulnerable to unauthorized access and other cybersecurity problems. Fortunately, secure…

Passwordless Authentication
In the ever-evolving landscape of cybersecurity, passwordless authentication has emerged as a compelling solution to address the shortcomings of traditional password-based authentication methods. However, despite its numerous advantages, there are still prevalent misconceptions surrounding passwordless authentication. In this blog, we…

Facial Recognition
Learn the benefits of face-based identity verification in financial services that safeguard customer information as well as secure and ease banking operations.Finance professionals are constantly battling fraudsters who continually devise new methods to bypass security checks. Even with EMV cards,…

Passwordless Authentication
Passwordless authentication is a new approach to online security that eliminates the need for traditional passwords. Instead, users can authenticate themselves using a variety of methods, such as biometrics, FIDO keys, or one-time codes. With the increasing number of data…

Security
In today’s interconnected world, the boundaries between physical and cyber threats are becoming increasingly blurred. As businesses and organizations rely more on digital infrastructure, they become more vulnerable to cyberattacks. However, it’s not just digital assets that are at risk…

Security
In today’s digital landscape, where cyber threats are evolving rapidly, ensuring robust security measures is paramount for organizations. Single Sign-On (SSO) has emerged as a convenient solution for users to access multiple applications with a single set of credentials, enhancing…

Passwordless Authentication
Passwords have been the primary method of authentication for decades. While they are convenient to use they possess significant weaknesses. Passwords can be stolen, hacked, or simply guessed by cybercriminals. In fact, most data breaches are caused by weak or…

Passwordless Authentication
In an era where the digital landscape is riddled with ever-evolving security threats, the limitations of traditional password-based authentication methods have become increasingly apparent. However, a transformative solution has emerged, revolutionizing the way users authenticate their identities and secure their…

Identity Management
According to a recent survey, 95% of companies are now adopting a multi-cloud approach, which means they try to rely on cloud services from at least two different providers to run their applications. Instead of depending on just one cloud…

Identity Management
With a predicted 82% growth globally in digital identity users by 2027, a collaboration between businesses, governments, and regulatory bodies is essential. Key Market Statistics – Digital Identity Apps Market Size in 2023: 2.3bn Market Size in 2027: 4.1bn 2023…

Access Control, Physical Access
RFID cards, or Radio-Frequency Identification cards, are used for tracking and identifying objects wirelessly. They consist of a small chip and antenna embedded in a plastic card, similar in size and shape to a credit card. The chip stores information…

Passwordless Authentication
In today’s digital landscape, the need for robust cybersecurity measures has never been more apparent. With cyber threats becoming increasingly sophisticated, traditional methods of authentication, such as usernames and passwords, are proving to be inadequate in protecting sensitive data and…

Facial Recognition
In today’s digital age, facial recognition technology has emerged as a powerful tool in law enforcement, revolutionizing how crimes are prevented, and investigations are conducted. The ability to analyze and identify individuals based on unique facial features has undoubtedly bolstered…
Health Attestation
The medical field is witnessing substantial network growth, making manual management of all network security points increasingly challenging. Moreover, overseeing a growing number of devices connected to a single network across various hospital departments is daunting. In this environment, manual…

Access Control
As security needs evolved beyond simple locks and keys, the concept of integrated access control emerged in the 1970s. Early systems were complex and expensive, often requiring in-house expertise for setup and maintenance. Enter system integrators, who played a crucial…

Passwordless Authentication
Privacy and security are the two major concerns of the modern tech era. With rapidly growing data on the globe, it becomes essential to ensure that its security is maintained at all expenditures. Even after implementing advanced security systems and…

Time & Attendance
Time-clocking systems have completely transformed how workplaces track and record employee work hours, bringing a new level of efficiency and accuracy to time management. Also known as a punch clock or time card machine, it is a device used to…

Security
Public Key Infrastructure Management, or PKI, is a set of rules for keeping digital certificates and encryption keys safe. It is a set of rules, procedures, hardware, and software that makes it possible to exchange data over networks in a…
Passwordless Authentication
Businesses are reconsidering their security strategies and approaches to prevent security breaches by malicious actors in the current global environment. Security threats are widespread and affect individuals, governments, and enterprises physically and digitally. When it comes to securing digital transactions…

Data Security
As businesses increasingly operate in a digital landscape, safeguarding sensitive information and ensuring secure communication is more crucial than ever. One powerful technology that addresses this need is Secure Shell (SSH). With over 20 million active SSH servers worldwide, it…

Access Control
According to Gartner, approximately 30% of critical infrastructure organizations will encounter a security breach that could cause a complete halt to operations by 2025. This makes it more important than ever to protect sensitive data. With the increasing use of…

Identity Management
Did you know that an alarming 30% of companies experienced an increase in “physical security incidents” in 2022? This staggering statistic underscores the pressing need for modern businesses to implement a robust visitor management solution as a vital component of…

Access Control
The industry of telemedicine and telehealth has seen a surge after the onset of the COVID-19 pandemic in 2020. A report published by McKinsey showed how telehealth use increased by 38 times in the recent pandemic. Even in 2023, we…

Workflow Automation
Did you know that companies worldwide spend an estimated $1.9 trillion annually on facility-related expenses? With such significant investments at stake, organizations are constantly seeking ways to optimize their workplace management processes. This quest for efficiency and cost-effectiveness has given…

Workflow Automation
In today’s rapidly evolving security landscape, effective visitor management is crucial for ensuring safety and security in various settings. Traditional manual visitor management processes rely on paper logs and manual data entry and are prone to errors, inefficiencies, and security…

Passwordless Authentication
In today’s fast-paced digital world, online security threats loom large. User frustrations with passwords continue to mount. Amidst this, a revolutionary solution has emerged — passwordless authentication. Imagine a world where you no longer need to rack your brain for…

Passwordless Authentication
In today’s digital age, security and user experience are paramount concerns for individuals and organizations. Traditional password-based authentication systems have long been the standard but come with inherent vulnerabilities and user frustrations.However, a new wave of passwordless authentication methods is…

Identity Management
The landscape of identity management is undergoing rapid transformation in response to the increasing demand for secure and efficient identity solutions in modern business. With advancing technology, the challenge of accurately identifying individuals becomes more complex. To remain at the…

Data Security, Facial Recognition
Facial recognition will become as ubiquitous as the fingerprint sensor on your phone. It’s just a matter of time. Jerry Yang, co-founder of Yahoo Imagine a world where your face becomes your key, unlocking doors, speeding up transactions, and personalizing…

Security
In the digital age we live in now, companies of all kinds have made job security a top concern. There are more hacking risks, data hacks, and privacy problems, so companies need to take steps to make their workplaces safer….

Security
In today’s world, where everything is becoming digital, businesses face security threats that put sensitive information and intellectual property at risk. As a result, companies are always looking for the best security solutions to protect their data. The global cloud…

Security
Cyberattacks are becoming more likely as more businesses are taking their operations online. Data can be stolen, money can be lost and even a company’s image can be hurt by a security breach. Consequently, organizations need to pay attention to…

Access Control
In the dynamic landscape of the digital age, the concept of Unified Identity has emerged as a key player in the realm of cybersecurity and user experience. Unified Identity refers to the seamless integration of various digital identifiers, such as…

Access Control
Zero Trust Architecture or ZTA is a cybersecurity approach that ensures an organization’s security by removing implicit trust and continuously verifying every digital interaction. It follows the principle of “never trust, always verify”. It aims to protect modern environments and…

Access Control
Access control is critical to any secure system, allowing users to control who can access their data and ensuring that sensitive information is kept private. Traditional access control systems rely on centralized authorities, such as login servers and identity providers,…

Time & Attendance
Time clock solutions refer to the various methods employers use to track employee working hours. These solutions are essential in the workplace, as they ensure accurate payment of wages and compliance with labor laws. However, there is an ongoing debate…

Facial Recognition
With the advent of smart devices, there came ways to secure your digital presence from unwanted access. This included manually typing in the PIN or drawing a pattern on our smart devices to unlock them. Besides being cumbersome, these methods…

Time & Attendance
Integrating time and attendance systems with physical access control systems has become essential for many workplaces, as it provides a more efficient and secure process for tracking employee attendance and controlling access to restricted areas. These two systems, although distinct,…

Access Control
In the dynamic landscape of technological advancements, the choice of the right wireless communication technology can be a critical decision for businesses seeking seamless connectivity and efficient operations. Radio-frequency identification (RFID), Near-Field Communication (NFC), and Bluetooth Low Energy (BLE) emerge…

Security
As the world becomes increasingly digitized, the security of a workplace has become more complex than ever before. The proliferation of cyber threats has created the need for organizations to establish stronger security measures that unify physical and cyber identities….

Access Control
In today’s digital age, data security has become a major concern for businesses of all sizes. One way to ensure data security is through access control systems that restrict user access to sensitive information. Two popular access control models are…

Physical Access, Identity Management
The Physical Access And Identity Management (PIAM) solutions used to be expensive and could only be afforded by companies with big budgets. But those days are far gone, now with the advancement of the PIAM industry and the use of…
Passwordless Authentication
Multi-factor authentication, or MFA, is a multi-step authentication process that protects individuals and organizations by checking a user’s identity with a combination of several factors. MFA adds extra security to tackle cyberattacks since third parties can steal, expose, or sell…

Access Control
Medical facilities work with sensitive patient data that, in any case, should not be leaked. As a result, medical facilities such as hospitals, laboratories, and others have to maintain strict regulatory compliance standards that include specialized security training for staff…

Passwordless Authentication
In today’s digital world, we rely heavily on technology for everyday tasks, such as shopping, banking, trade and communication. Increased reliance on technology increases the risk of security breaches and fraud. Behavioral biometrics has emerged as a new approach to…

Access Control
Commercial property owners are responsible for ensuring their tenants have a positive experience in their buildings. Providing a great tenant experience is essential for tenant satisfaction and retention, attracting new tenants, and maintaining a good reputation in the industry. Understand…

Access Control
Online security and privacy have become critical concerns in the modern digital world, where the internet is vital to our lives. Proxy servers are an underutilized tool for businesses of all sizes. They can help to protect sensitive data, improve…

Oloid – blogs
In today’s fast-paced, data-driven world, organizations of all sizes are grappling with the challenges and opportunities presented by the immense volume of information at their disposal. The importance of effective data governance cannot be overstated, as it is the key…

Oloid – blogs
Embarking on an on-premise to cloud migration journey? Discover best practices to overcome common challenges, from data security and connectivity to application compatibility, cost, and potential downtime. Learn how to meticulously plan your migration, from understanding assets and dependencies to…

Access Control
Are you in charge of managing access control systems for multiple sites? We know it can be overwhelming, but don’t worry, we’ve got you covered! In this article, we’ll share the top 10 best practices that can make managing multi-site…

Time & Attendance
Wage theft and time theft are two forms of illegal practices that impact employees and employers. Wage theft occurs when an employer fails to pay workers the wages they have earned, while time theft occurs when employees are paid for…

Time & Attendance
In today’s fast-paced business world, effective workforce management is essential for organizational success. One critical aspect of this management is tracking and recording employee work hours accurately. Manual processes can be time-consuming, error-prone, and cumbersome, leading to productivity losses and…

Oloid – blogs
In today’s digital world, the security of our personal and business information has become more critical than ever. With the increasing risk of cyber-attacks and data breaches, protecting sensitive information has become a top priority for individuals and businesses. One…

Facial Recognition
In our contemporary, fast-paced world, the need for security and convenience has reached a paramount status in nearly every facet of daily life. The advent of facial authentication, boasting an astonishing accuracy rate of up to 99.97%, stands as a…

Oloid – blogs
Introduction In today’s interconnected world, where businesses rely heavily on technology to conduct their operations, the risk of cyber-attacks has reached alarming proportions. Cybercriminals are becoming increasingly sophisticated, exploiting vulnerabilities in computer systems and networks and causing substantial financial losses…
Oloid – blogs
Secure access control is of primary importance as organizations worldwide transition back to the workplace after remote work. The global COVID-19 pandemic has reshaped security needs, emphasizing the necessity for contactless features integrating biometric and facial recognition technologies. Recent technological…

Oloid – blogs
In the digital age we live in today, it has never been more important to protect private information with strong security methods. Password-based verification has been the norm for decades — one that has brought with it several problems. The…

Oloid – blogs
In today’s fast-paced business world, efficient time and attendance tracking are critical to workforce management. Gone are the days of relying on manual processes prone to errors, inefficiencies, and time theft. Businesses are turning to the power of security workflow…

Oloid – blogs
With the surge in service-based applications on smartphones and computers, user authentication has become a staple. Consequently, users find themselves juggling multiple usernames and passwords for different services. This has led to a common dilemma: creating complex passwords that are…

Oloid – blogs
Face authentication technology is utilized globally to deter crimes, shield the public from fraud, and enhance customer experiences. This innovative authentication method is being adopted across many industries, although it remains somewhat unfamiliar and high-tech to some individuals. “Your face…

Oloid – blogs
In today’s world, ensuring the safety and well-being of individuals in various settings such as office buildings, schools, or hospitals is vital. Manual occupancy management can be resource-intensive and error-prone. Automation in this area streamlines security operations and fosters a…
Data Security
Many businesses leverage digital tools to operate in the modern digital landscape. While this technology has undoubtedly streamlined business operations, it has paved the way for cybercriminals to exploit vulnerabilities and steal sensitive information, making cybersecurity a critical concern for…

Oloid – blogs
In the current digital world, passwords have been the primary way to protect our internet accounts for a long time. However, the limits and weaknesses of passwords are becoming more evident, leading to the rise of authentication options that don’t…

Oloid – blogs
Since its introduction in November 2022, ChatGPT has rapidly emerged as a groundbreaking AI-driven tool, capturing the interest of tech enthusiasts and professionals alike. Its versatility allows users to harness its capabilities for various tasks, from composing eloquent speeches and…

Oloid – blogs, Time & Attendance
Accurate tracking of employee attendance and hours worked is essential for ensuring fair compensation and efficient payroll management. However, buddy clocking remains an issue for many employers. Buddy clocking happens when an employee clocks in or out for a colleague,…

Oloid – blogs
The traditional password-based authentication system is challenging today’s digital landscape. While it offers security to our online accounts, it also requires us to manage multiple complex passwords, risking data and digital safety. The Verizon data breach incident report for 2022…

Oloid – blogs
With the advancement of technologies, face-based recognition systems have come to fill many needs of human society. From unlocking smartphones to surveillance systems in public spaces, face-based recognition has brought convenience and enhanced security. However, the growing adoption of this…

Oloid – blogs
In this digital age, sensitive information and personal data are at constant risk of compromise, and robust security measures are necessary. Traditional authentication methods, such as passwords and PINs, are no longer sufficient to protect against advanced cyber security threats….

Access Control
In recent years, remote work has experienced a significant popularity surge, necessitating effective solutions that enable seamless collaboration, access to work environments, and secure data management. Cloud-based solutions have emerged as a key component in empowering remote workforces, offering flexibility,…

Access Control
In a rapidly changing world, physical security isn’t immune to the sweep of innovation. Today, the future of this critical sector rests firmly on the shoulders of advanced access control systems. These technologies, rooted in integrating Artificial Intelligence, IoT, and…

Access Control
In today’s hyper-connected digital era, an unprecedented volume of data is created, exchanged, and stored daily. According to Verizon, amidst this enormous data flux in 2023, it has been found that more than 83% of data breaches involved external actors,…

Time & Attendance
According to a study by the American Payroll Association, buddy clocking may be responsible for as much as 7% of business payroll expenditures.The phenomenon known as buddy clocking, wherein employees clock in or out on behalf of tardy or absent…

Facial Recognition
In a world where technology continues pushing the boundaries of what we thought was possible, facial recognition technology has emerged as a game-changer. Imagine a world where a mere glance can grant you access to your personal devices and security…

Access Control
Access control is vital in today’s organizations, ensuring the security of physical and digital assets. As businesses continue to digitize their operations and expand their digital infrastructure, the need for scalable access control solutions becomes increasingly critical.A recent survey reveals…

Passwordless Authentication
In today’s digital landscape, the demand for robust authentication methods has never been greater. Traditional password-based authentication, while widely used, comes with inherent vulnerabilities and usability challenges. As a solution to these shortcomings, passwordless authentication has emerged as a more…

Security
The concerning surge in cyber attacks in recent years has propelled cybersecurity to the forefront of headlines. According to current cybersecurity news, cybercrime incurred a cost of $6 trillion in 2022, with predictions of further escalation in 2023.As we embark…

Access Control
Proximity cards have emerged as a popular choice in access control systems, revolutionizing the way organizations secure their premises. According to market research, the global proximity cards market is projected to exceed $2 billion by 2026, with a compound annual…

Mobile Access
Accessing secured and restricted areas in the past involved the use of key cards, printed documents, and physical verification procedures, which often resulted in delays, productivity loss, and inconvenience. However, the advancements in Information and Communications Technology (ICT) have revolutionized…

Data Security
Encryption is one of the most important parts of a company’s cybersecurity approach. Encrypting data in the cloud not only prevents unauthorized use of the data but also mitigates other serious security risks, including: Adherence to applicable laws and policies…

Security
According to a report published by US Bureau of Labor Statistics, 2.61 Million nonfatal workplace safety incidents took place in 2021. Businesses need to ensure the safety of their workplaces, being mindful of dangers such as computer hacking and internal…

Security
Explained: The fundamentals of Public Key Infrastructure (PKI) Are you familiar with encryption, digital certificates, and Public Key Infrastructure (PKI)? If these terms are unfamiliar to you, don’t worry. We’ll delve into these concepts together and shed some light on…

Identity Management
Facial recognition technology is being used in more places than ever before. It offers convenience, but it also raises ethical questions – how should the technology be used, and how can we protect privacy?This article will look at the best…

Data Privacy, Data Security
In the digital age, data protection is more important than ever, especially when safeguarding your employees’ personal information. In this post, we’ll cover the basics of data protection and provide tips to help keep your employees’ data safe. What is…

Security
Operational security keeps private information safe by looking at things from a hacker’s point of view. The goal is to find any possible weak spots and take the steps needed to protect against any possible dangers. OPSEC was developed by…

Access Control
Businesses and organizations are increasingly turning to cloud-based access control systems to efficiently manage access to their facilities, equipment, and data. These systems offer a flexible and scalable solution that can be accessed from any location with an internet connection….

Access Control
Access control is a critical component of any organization’s security strategy, and it plays a vital role in ensuring that sensitive information and systems are accessed only by authorized personnel. This approach significantly reduces the risk of data breaches or…

Access Control
As a property manager, a crucial responsibility is to ensure tenants’ safety and well-being. A proven method to achieve this is by implementing access control systems that regulate entry and exit to the property.Contemporary access control systems offer a sense…

Security
Corporate security teams are responsible for safeguarding a company’s physical and digital assets, as well as ensuring the safety of its employees. However, as technology advances and threats become more sophisticated, corporate security teams are faced with a range of…

Access Control
Physical Access Control Systems (PACS) have been an essential aspect of physical security for decades. Access control has come a long way from the early days of keys and locks to the modern era of biometric and cloud-based access control…

Security
Facial recognition and facial authentication are two related technologies that have become increasingly popular in recent years. They both involve the use of computer algorithms to analyze images of faces, but they serve different purposes. In this blog post, we…

Identity Management
With everything now connected to the internet in the 21st century, it is essential for businesses and companies to ensure a secure work environment. Security threats can be disastrous and potentially devastating. Therefore, continuous reinforcement through biometric identification is crucial…

Identity Management
Single Sign-On (SSO) is a technology that allows users to authenticate their identity once and then access multiple applications and systems without having to re-enter their credentials. Instead of managing separate login credentials for each application, users can authenticate themselves…

Identity Management
In today’s digital world, organizations of all sizes and types rely on numerous applications, systems, and devices to manage their business operations. However, with increased dependence on technology comes the risk of data breaches and unauthorized access to sensitive information….

Health Attestation
The last few years have brought about significant changes that have led companies to prioritize the health and safety of their employees. Governments and health regulatory authorities have implemented strict measures and regulations to ensure workplace well-being, and technology has…

Time & Attendance
Time and attendance tools are important for any business that wants to handle its employees well, keep track of their attendance and punctuality, and make sure that payroll is processed correctly. With the development of technology, time and attendance systems…

Access Control
In a world where security risks are escalating, and data breaches are becoming a pressing concern, organizations must adopt advanced access control systems. 30% of critical infrastructure organizations worldwide are predicted to experience a security breach by 2025, according to Gartner. Businesses…

Access Control
Over the last century, technological advancements have closely intertwined with business progress. However, as technology continues to rapidly infiltrate industries worldwide, there is a parallel increase in security concerns. This phenomenon has led to physical access control becoming a critical…

Data Privacy, Data Security
Remote work has become increasingly common in recent years, and the COVID-19 pandemic has accelerated this trend. In fact, a recent study found that 43 percent of companies allow some employees to work remotely at least part-time. And that number…

Access Control
Are you looking for a secure and centralized way to manage your physical access systems? Consider a cloud-based access control system that provides centralized management, real-time updates, visibility, cloud wiring, diagnostics, and other features at a lower cost than traditional…

Access Control
Access control systems have become increasingly popular over the years, as businesses and organizations look to improve their security and restrict access to certain areas. However, different businesses have distinct requirements based on their size, status, and criticality, all of…

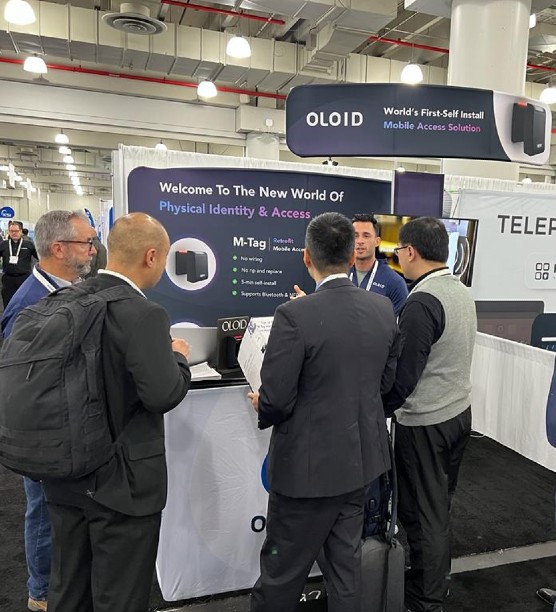
Physical Access
At the recent ISC West event in Las Vegas, OLOID unveiled its newest product, OLOID Workflows. The product is designed to help organizations automate physical security and business operations using no-code/low-code workflows, allowing them to extract more value from their…

Security
In today’s digital age, cloud computing has become increasingly popular, with businesses of all sizes adopting cloud-based solutions to improve their operations. Two popular cloud computing services are SaaS and SECaaS, but what are they, and how do they differ?…

Access Control
Using traditional locks and keys has ensured secure entry into buildings for generations. However, as a result of COVID-19, the functions and duties of property managers are undergoing significant transformation. A rise in the use of new technologies can be…

Access Control
In the realm of running a business, one of the most critical aspects is the maintenance of a safe workplace. Ensuring the safety and security of all employees, data, hardware, networks, software, and physical property is paramount to the smooth…

Access Control
Access management systems are critical components of any organization’s security infrastructure. However, these systems can become outdated over time, making them less effective in providing the necessary level of security. Retrofitting access solutions is a cost-effective and practical way to…

Data Security
Cybersecurity is an ever-evolving field, and we must remain vigilant to stay ahead of cyber threats. In recent years, we saw an increase in ransomware attacks, cyber attacks on critical infrastructure. The attack on the Colonial Pipeline in 2021 highlighted…

Security
The ever-evolving landscape of cyber threats is becoming increasingly challenging, particularly for businesses trying to remain competitive in today’s economy. Cyberattacks come in a variety of forms, ranging from basic malware to sophisticated, targeted attacks. This heightened complexity can have…

Access Control
Physical access control systems are a critical component of any security strategy. They play a vital role in regulating access to buildings, facilities, and sensitive areas, ensuring that only authorized personnel are allowed in. These systems are designed to protect…

Access Control
As we continue to move towards a more connected and technologically advanced world, access control systems are evolving at a rapid pace to keep up with the changing security landscape. From biometric authentication to cloud-based solutions, the access control industry…

Security
Commercial buildings are often bustling with activity, with numerous employees, customers, vendors, and visitors entering and exiting the premises on a daily basis. With valuable assets and sensitive information at stake, it’s crucial to ensure that commercial buildings have robust…

Access Control
Access control systems have become an essential part of modern security infrastructure for businesses of all sizes. These systems provide a way to secure physical access, by controlling who has permission to enter and when. With the advent of cloud-based…

Access Control
In today’s world, security is a top priority for both residential and commercial properties. Traditional lock and key systems have been the norm for centuries, but they can be inconvenient and sometimes less secure. With advancements in technology, keyless door…

Security
As technology continues to advance, organizations face increasingly complex security threats, both in the physical and digital realms. While physical security and cybersecurity are often treated as separate issues, they are closely interconnected and the boundaries between physical security and…

Access Control
The emergence of smart and electronic locks offers businesses a range of new features and levels of security. But which type of lock is best? An electronic lock, also known as an electrified lock, is a lock that uses an…

Access Control
The choice between retrofitting access solutions and replacing your existing physical access control system (PACS) depends on a variety of factors, including the current state of your system, your budget, and your security needs. Retrofitting access control solutions Before we…

Access Control
The RFID market is projected to grow to USD 35.6 billion by 2030, with a forecasted CAGR of 11.9% during the period. The significance of these figures is that technological advancements have had a major impact on the security industry.However,…

Access Control
The access control industry has experienced a significant growth in recent years. The increasing demand for security and surveillance measures, coupled with technological advances, has increased the number of businesses and organizations investing in access control systems. The industry is…

Access Control
As communication and access to information have expanded, so has public concern over the issue of protecting personal data. As a result, there has been a steady rise in the importance of offline workplace security. Many businesses nowadays have implemented…

Data Privacy
The General Data Protection Regulation (GDPR) is a regulation in European Union (EU) law on data protection and privacy for all individuals within the EU and the European Economic Area (EEA). The regulation replaces the 1995 Data Protection Directive and…
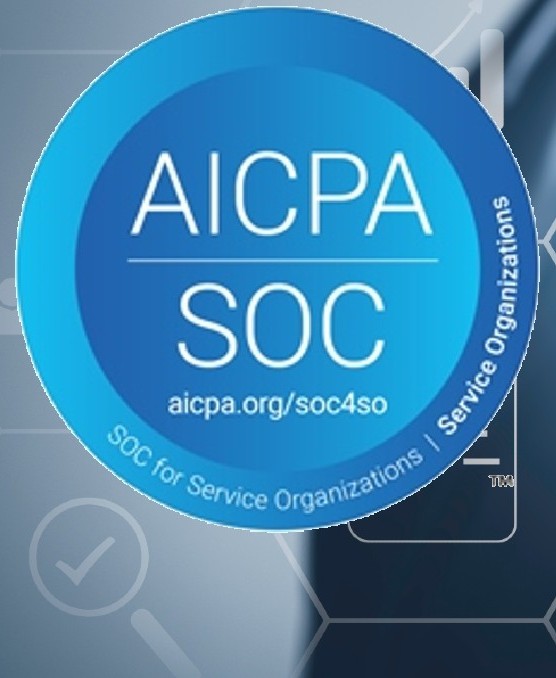
Data Security
OLOID is proud to announce that it has successfully completed its Service Organization Control (SOC) 2 Type II certification. This certification is a validation of OLOID’s adherence to the most stringent industry standards for data security and privacy, reinforcing its…

Data Privacy
Employers have a duty to secure employee data stored, and the role of HR in safeguarding workers’ information cannot be emphasized enough. This division holds confidential personal information, such as Social Security numbers, bank information, health records, and addresses. Statista reports…

Data Security
Information and communications technology is an integral part of our lives. Without these advanced systems, it would be difficult for governments, businesses, and individuals to function properly in this digital age. However valuable as they may be, these technologies are…

Identity Management
Identity and Access Management (IAM) is a framework for managing and protecting the identities of users, devices, and other resources in an organization. It is a crucial aspect of modern-day security. Here’s a detailed overview of identity and access management,…

Physical Access
Artificial Intelligence (AI) is a rapidly growing from where it stated way back in 1950’s at a workshop in Dartmouth College. One area that has seen a significant impact in recent years is physical access control. The physical access control systems are…

Mobile Access
As the world becomes more mobile, individuals and organizations need to incorporate mobile devices into their living and working environments. ‘smart homes’ and ‘smart workplaces’ are becoming common terms. Access control systems are an important part of most organizations and…

Access Control
In 2019, the total value of physical security goods manufactured worldwide was $34.3 billion, an 8.5% rise from 2018. The security market has been thriving for the past five years, expanding at a CAGR of 7.2%. The access control market…
Security
Artificial intelligence (AI) has the potential to revolutionize the field of cybersecurity, providing new tools and techniques to detect and prevent cyberattacks. However, there are also concerns that AI could be used by attackers to automate and escalate their attacks,…

Identity Management, Data Security
Driven by decentralization, cloud usage, and remote work, digital transformation and the subsequent evolution of identity in the workplace have revealed that identity and access management has outgrown traditional security measures and offers significant threats. To protect workers and businesses,…

Oloid – blogs, Mobile Access
The rapid development of digital technology has provided us with many automated alternatives to previously manual processes. It is hard to think about a time when we did not have mobile phones. Mobile phones have become a vital part of…

Identity Management
The concept of Identity management (IdM), also known as identity and access management (IAM or IdAM), has its roots in the development of directories, such as X.500, where a namespace serves to hold named objects that represent real-life “identified” entities,…
Access Control, Mobile Access
Cloud-based access management, security, and mobility were amongst the most resounding themes at the recently concluded ISC East, a flagship event hosted by the International Security Conference, in collaboration with the Security Industry Association (SIA), at the Javits Center, New…

Oloid – blogs, Access Control, Physical Access, Identity Management
At the recently concluded identity event – Oktane22, OLOID successfully presented a unique solution of converging the physical identity with digital credentials to give a passwordless means to deskless workers to login into employee applications and other interfaces. While passwordless…

Access Control, Physical Access
Workplaces are undergoing a digital transformation. Enterprises need to ensure that newly adopted tools and technologies have secure and protected access for users. Various security techniques can be used to protect systems, devices, applications, and even machines. Access control is…

Access Control
In recent years, the technology of biometrics has taken a giant leap and its applications have expanded significantly. One of the most significant applications of biometrics is in the field of access control systems. A biometrics access control system uses…

Access Control, Data Security
The concept of physical office space is changing rapidly. The global pandemic resulted in severe lockdowns worldwide, forcing organizations to employ containment measures. As businesses return to traditional workplaces, there is growing interest in the cost-effective option of sharing workspaces…

Data Security
The total amount of data on the internet is flabbergasting. Estimated at 79 zettabytes (one zettabyte is approximately one billion terabytes) in 2020, the total amount of data is expected to rise to 175 zettabytes by 2025 per Seagate UK….

Access Control
One of the most crucial things to ensure your workplace security is to have a robust physical access control system. Powerful software paired with an access control device, card access system, or security system allows you to track who passes…

Mobile Access
The past few years have completely upturned workplace dynamics and compelled us to push the limits to accommodate work-from-home options. Businesses across the globe have revised their standards to adopt a virtual, work-from-home culture. With the availability of vaccinations, the…

Data Privacy
Data access and data storage are prevalent in the business world — and they carry risk. There is a good reason that data has been called “the new black gold.” As increasingly granular data becomes more easily available, many new…

Access Control
Introduction Historically, access control was partially accomplished through keys and locks. When a door is locked, only someone with a key can enter through the door, depending on how the lock is configured. Mechanical locks and keys do not allow…

Access Control
The evolution of access control and identity management has been a long, slow journey. About ten years ago, laptops introduced the first fingerprint readers. And it was another five years before those readers became common. An entire decade passed before…

Physical Access
Archaic proximity cards are losing the hegemony to retrofit & identity-based mobile access control systems. Enterprises transitioning to modern-day access control systems are reaching tangible benefits downstream. Proximity cards have been the primary access mode for many businesses and organizations…

Physical Access
Multimodal authentication is a process for capturing biometric traits apart from just face and voice. Also known as multimodal biometrics, this technology combines different types of biometrics, sometimes simultaneously, in a multi-factor solution that offers a multitude of authentication options….

Mobile Access
There is a lot of talk about mobile credentials and their impact on the future of authentication, but the details are often unclear. Whether you’re just starting out in the world of mobile authentication or looking for ways to improve…

Vaccine Management
As the year 2019 was coming to an end, horror was unleashed on the entire world in the form of COVID-19. None of us could have imagined the magnitude of destruction and disruption it would cause in the next 2-3…
Oloid – blogs
Following is the text from the video chat between Aradhna Gupta, Founder of Access Alts, and Mohit Garg, CEO Oloid, who talks in detail about Oloid being an identity platform targeted for deskless workers. What is Oloid? Oloid is an…

Physical Access
Last week, as my family and I were excitedly watching the images of Richard Branson and his crew penetrate the edge of space. Amidst all the excitement, I couldn’t help but wonder about the countless hours of persistent work and…

Time & Attendance
OLOID’s facial recognition-based and contactless time and attendance clocking, wellness attestation, mask detection and vaccination status check application is accurate and easy to use. Oloid seamlessly integrates with ADP Workforce Now® Essential Time. The turnkey integration is available on ADP®…

Time & Attendance
The construction industry has unique requirements for the safety, security, and mobility of personnel, contractors, resources, and equipment. Construction projects can be multi-year projects that use heavy duty machinery, hazardous equipment and supplies. Furthermore, these machinery, resources, and personnel can…
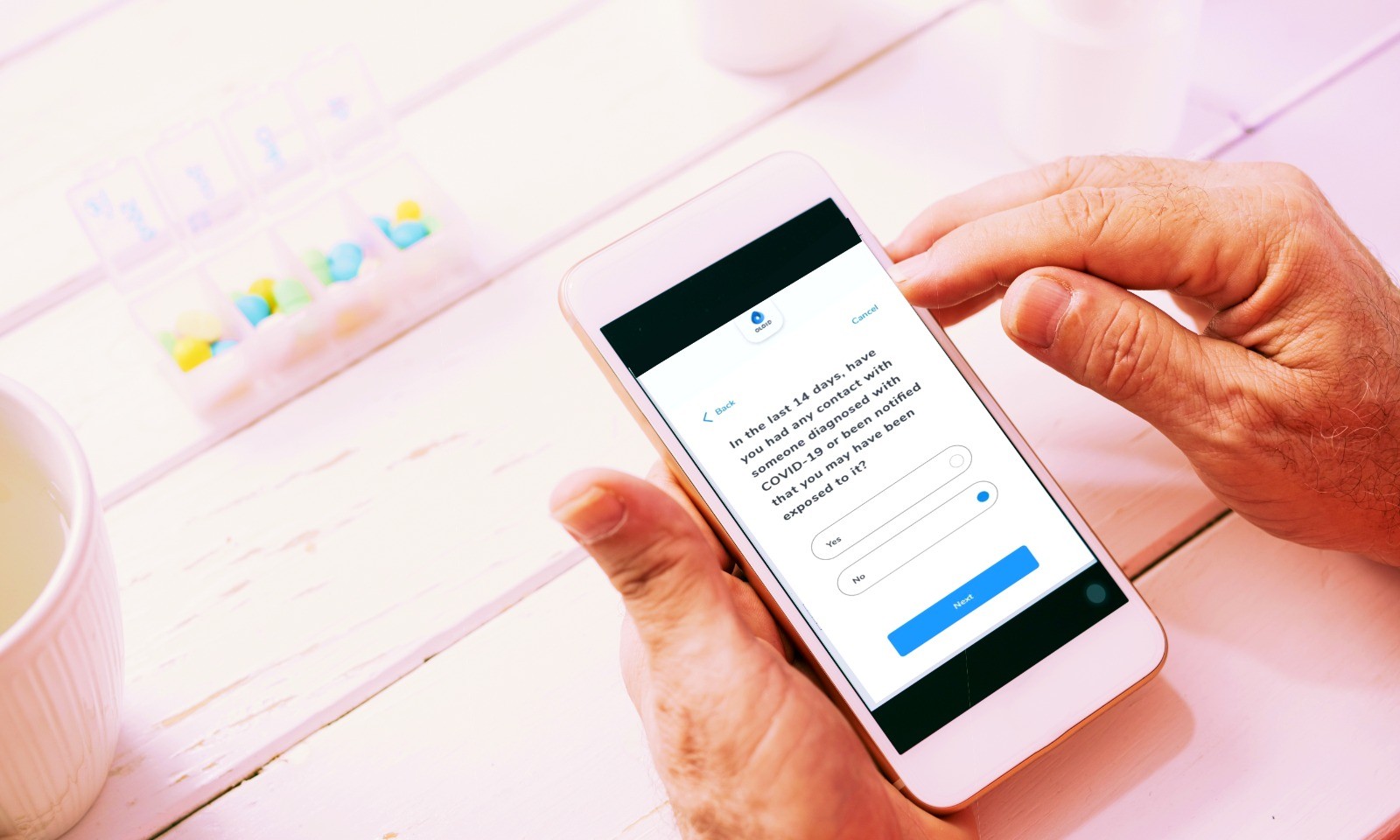
Access Control
Oloid Certify is a QR-code based contactless wellness attestation solution, which is helping workplaces stay safe during this pandemic by administering a health questionnaire. Employees and visitors can respond to screening questions regarding their whereabouts and health from their personal…

Identity Management
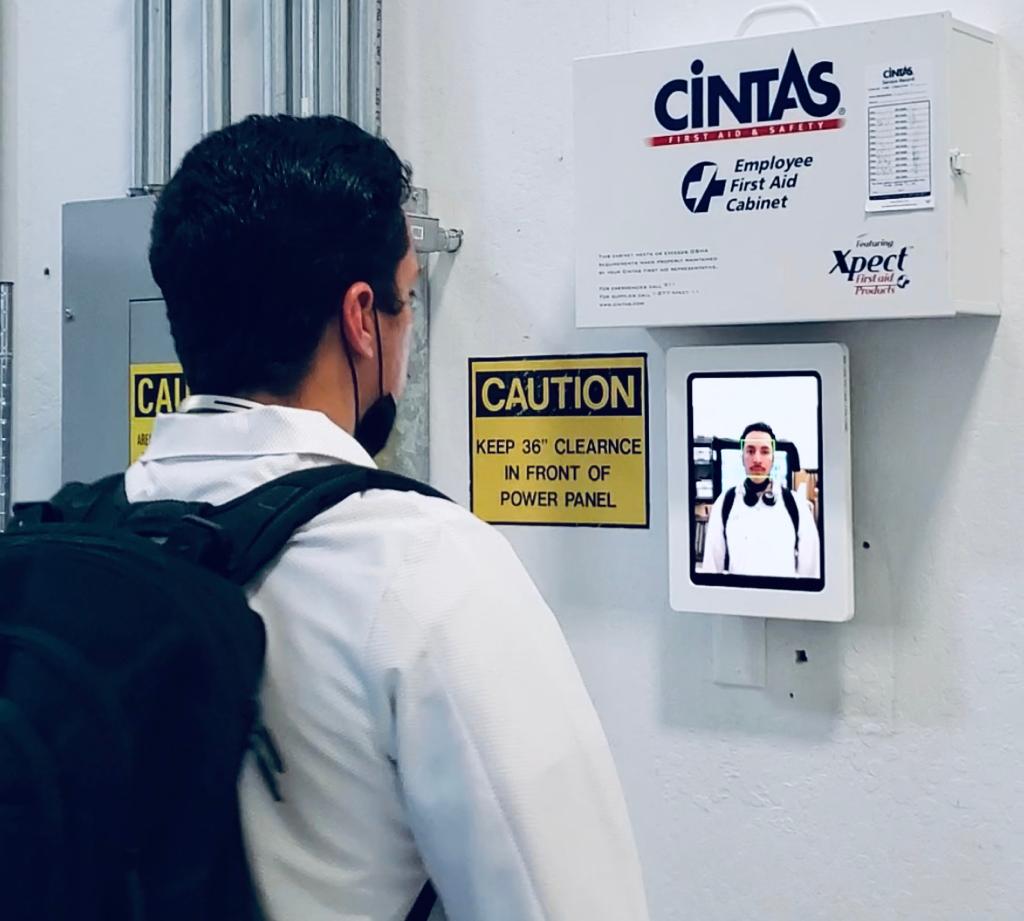
Contactless biometric technology is not new. However, in recent months, we have seen a steep rise in the use of contactless technology in business operations. This is so because contactless interactions in work environments have become crucial at the moment…

Data Privacy
Data privacy considerations at workplace Most states in the US are entering the final phases of the reopen plan that seeks to gradually re-establish business operations in light of the ongoing COVID-19 pandemic. While a welcome sign for many businesses…

Oloid – blogs
Ensuring the safety of people and assets is vital in our increasingly connected world. Whether in public spaces or private enterprises, robust physical security is essential to guard against theft, damage, and acts of terrorism. Fortunately, advancements in technology, particularly…

Oloid – blogs
In an era defined by digital transformation and ever-evolving cyber threats, the traditional approach to user authentication is facing unprecedented challenges. Password-based systems, once the cornerstone of digital security, are increasingly proving inadequate in safeguarding sensitive information against sophisticated cyber…

Oloid – blogs
In today’s fast-paced, data-driven world, organizations of all sizes are grappling with the challenges and opportunities presented by the immense volume of information at their disposal. The importance of effective data governance cannot be overstated, as it is the key…

Oloid – blogs
Embarking on an on-premise to cloud migration journey? Discover best practices to overcome common challenges, from data security and connectivity to application compatibility, cost, and potential downtime. Learn how to meticulously plan your migration, from understanding assets and dependencies to…

Oloid – blogs
In today’s digital world, the security of our personal and business information has become more critical than ever. With the increasing risk of cyber-attacks and data breaches, protecting sensitive information has become a top priority for individuals and businesses. One…

Oloid – blogs
Introduction In today’s interconnected world, where businesses rely heavily on technology to conduct their operations, the risk of cyber-attacks has reached alarming proportions. Cybercriminals are becoming increasingly sophisticated, exploiting vulnerabilities in computer systems and networks and causing substantial financial losses…
Oloid – blogs
Secure access control is of primary importance as organizations worldwide transition back to the workplace after remote work. The global COVID-19 pandemic has reshaped security needs, emphasizing the necessity for contactless features integrating biometric and facial recognition technologies. Recent technological…

Oloid – blogs
In the digital age we live in today, it has never been more important to protect private information with strong security methods. Password-based verification has been the norm for decades — one that has brought with it several problems. The…

Oloid – blogs
In today’s fast-paced business world, efficient time and attendance tracking are critical to workforce management. Gone are the days of relying on manual processes prone to errors, inefficiencies, and time theft. Businesses are turning to the power of security workflow…

Oloid – blogs
With the surge in service-based applications on smartphones and computers, user authentication has become a staple. Consequently, users find themselves juggling multiple usernames and passwords for different services. This has led to a common dilemma: creating complex passwords that are…

Oloid – blogs
Face authentication technology is utilized globally to deter crimes, shield the public from fraud, and enhance customer experiences. This innovative authentication method is being adopted across many industries, although it remains somewhat unfamiliar and high-tech to some individuals. “Your face…

Oloid – blogs
In today’s world, ensuring the safety and well-being of individuals in various settings such as office buildings, schools, or hospitals is vital. Manual occupancy management can be resource-intensive and error-prone. Automation in this area streamlines security operations and fosters a…

Oloid – blogs
In the current digital world, passwords have been the primary way to protect our internet accounts for a long time. However, the limits and weaknesses of passwords are becoming more evident, leading to the rise of authentication options that don’t…

Oloid – blogs
Since its introduction in November 2022, ChatGPT has rapidly emerged as a groundbreaking AI-driven tool, capturing the interest of tech enthusiasts and professionals alike. Its versatility allows users to harness its capabilities for various tasks, from composing eloquent speeches and…

Oloid – blogs, Time & Attendance
Accurate tracking of employee attendance and hours worked is essential for ensuring fair compensation and efficient payroll management. However, buddy clocking remains an issue for many employers. Buddy clocking happens when an employee clocks in or out for a colleague,…

Oloid – blogs
The traditional password-based authentication system is challenging today’s digital landscape. While it offers security to our online accounts, it also requires us to manage multiple complex passwords, risking data and digital safety. The Verizon data breach incident report for 2022…

Oloid – blogs
With the advancement of technologies, face-based recognition systems have come to fill many needs of human society. From unlocking smartphones to surveillance systems in public spaces, face-based recognition has brought convenience and enhanced security. However, the growing adoption of this…

Oloid – blogs
In this digital age, sensitive information and personal data are at constant risk of compromise, and robust security measures are necessary. Traditional authentication methods, such as passwords and PINs, are no longer sufficient to protect against advanced cyber security threats….

Oloid – blogs, Mobile Access
The rapid development of digital technology has provided us with many automated alternatives to previously manual processes. It is hard to think about a time when we did not have mobile phones. Mobile phones have become a vital part of…

Oloid – blogs, Access Control, Physical Access, Identity Management
At the recently concluded identity event – Oktane22, OLOID successfully presented a unique solution of converging the physical identity with digital credentials to give a passwordless means to deskless workers to login into employee applications and other interfaces. While passwordless…
Oloid – blogs
Following is the text from the video chat between Aradhna Gupta, Founder of Access Alts, and Mohit Garg, CEO Oloid, who talks in detail about Oloid being an identity platform targeted for deskless workers. What is Oloid? Oloid is an…